What is a BIN attack? How it works, warning signs, and how to prevent it

Online payments have made shopping faster and more convenient, but they’ve also created new opportunities for fraud. One of them is a Bank Identification Number (BIN) attack, a method fraudsters use to identify valid payment card details and attempt fraudulent transactions.
Understanding what BIN attacks are and how they affect online payments can help merchants and cardholders recognize warning signs and reduce the risk of fraud.
Please note: This information is for general educational purposes and not financial or legal advice.
What is a BIN attack?
A BIN attack is a type of payment card fraud in which criminals use automation and a known BIN to generate plausible card numbers and test combinations of payment data, such as Primary Account Numbers (PANs), expiration dates, and security codes, in order to identify valid card details. The BIN is the first set of digits (according to Mastercard, the first 6 to 11 digits) on a payment card and identifies the card issuer and card program, while the PAN is the full card number used to process a transaction.
The goal of a BIN attack is to identify valid card details that can later be used in fraudulent online transactions.
Although it’s related to other forms of payment card fraud, a BIN attack is a more specific method with a different purpose. For example, card testing usually involves attempting small or low-risk transactions to confirm that card details still work, and carding involves using stolen card details to make fraudulent purchases, often for easy-to-resell goods such as gift cards.
Credit card fraud is the broader category that includes many forms of illegal card activity, such as account takeover, skimming, and fraudulent applications.
How common are BIN attacks?
Exact public figures for BIN attacks are limited, but they fall under the broader categories of enumeration (the automated guessing and testing of card details to find valid accounts) and account-testing attacks, which remain a major payment fraud threat. The Visa Biannual Threats Report (2025) has described enumeration as a prolific global problem and reported that it led to about $1.1 billion in follow-on fraud over a one-year period.
In a separate six-month window, Visa reported hundreds of millions of suspected enumeration-attack transactions worldwide, with enumerated transaction volume up 22% from the previous six months.
Industries that process high volumes of card-not-present transactions are often attractive targets for BIN-related attacks. Visa’s public reporting has identified merchant categories such as miscellaneous and specialty retail stores, eating places, and restaurants among heavily targeted categories for enumeration activity.
Also read: How to make secure online payments?
How does a BIN attack work?
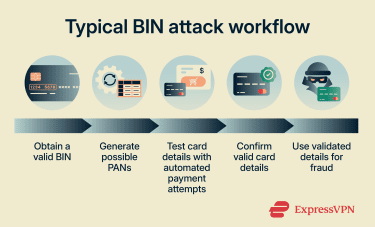
A BIN attack usually follows a structured process:
- Identifying a real BIN: The attack begins with a genuine BIN, which attackers may obtain from exposed card data, compromised systems, or other payment data sources. They may also have the card’s expiration date, which helps narrow the range of details they need to test.
- Generating possible PANs: Using the BIN as a starting point, criminals use a program to generate the remaining digits of possible PANs and pair them with other payment data values. The goal is to identify combinations linked to active accounts.
- Testing card details at scale: Attackers then combine the generated PANs with other payment values, such as expiration dates, security codes, or billing data, and submit them through online checkout pages or payment forms. This step is often automated using bots or scripts, enabling many authorization attempts in a short time.
- Confirming valid cards: If a small authorization is approved, the attacker knows that the tested combination of card details is sufficient to pass that merchant’s checks. This confirms that the card details may be usable in later fraud attempts.
- Exploiting confirmed cards: Once valid card details are identified, they can be used for fraudulent card-not-present transactions, including higher-value purchases.
How are BIN attacks detected?
BIN attacks are rarely identified through a single suspicious transaction. Instead, they're more often detected through patterns in payment activity, such as a sudden rise in low-value authorization attempts, unusually high decline rates, or numerous transactions tied to the same or similar BIN range within a short period.
Detection systems may also look for signs of automation, including unusually high transaction velocity, repeated failed attempts from the same IP address or device, or activity that doesn’t match a merchant’s normal checkout behavior. Taken together, these signals can suggest that card details are being tested systematically rather than used for legitimate purchases.
What to do when you suspect a BIN attack
If you notice unfamiliar charges, repeated authorization alerts, or transactions you don’t recognize, the most important step is to contact your bank or card issuer immediately.
- Report the suspicious activity to your bank: Use the phone number on the back of your card, your banking app, or the issuer’s customer support channel. Reporting it promptly gives the bank a chance to review the transactions, restrict further use of the card if needed, and determine whether the card details may have been compromised.
- Request that the card be replaced if necessary: If the issuer believes the card details may have been exposed, it will usually cancel the existing card and issue a replacement with a new card number. Replacing the card helps prevent further misuse of the compromised details.
- Monitor the account for additional transactions: Continue checking your account statements, banking app, or transaction alerts while the bank investigates. Spotting suspicious activity early can help limit further misuse and ensure unauthorized transactions are reported quickly.
- Dispute any unauthorized charges: If fraudulent transactions appear on your statement, notify the card issuer promptly so it can review them and initiate a dispute if needed.
- Report the incident through official fraud-reporting channels if needed: If the activity involves identity theft, multiple compromised accounts, or significant financial loss, it may also make sense to report it through official channels, such as the relevant government consumer-protection or identity-theft reporting service in your country.
Impact of BIN attacks
BIN attacks can cause harm even before a fraudulent purchase is completed. Because the attack is designed to identify valid card details at scale, the first impact often appears in payment systems, fraud operations, and authorization data rather than in a single obvious transaction.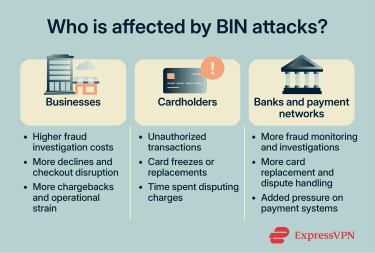
For businesses
For businesses, BIN attacks can increase failed payment attempts, put pressure on fraud teams, and raise processing costs, especially when merchants are charged for large volumes of failed authorizations. The 2025 Association for Financial Professionals (AFP) Payments Fraud and Control Survey found that 79% of organizations experienced attempted or actual payments fraud activity in 2024. If attackers successfully validate card details, businesses may also face chargebacks, customer frustration, and damage to trust.
For cardholders
For cardholders, the effects may include unauthorized charges, card declines, temporary account restrictions, or the issuance of replacement cards after suspicious activity is detected. Even when fraudulent charges are reversed, the process can still be inconvenient and stressful, especially if the card is used for recurring payments or everyday spending.
For banks and card networks
Banks, issuers, acquirers, and card networks may also absorb a large share of the impact. They may need to investigate suspicious authorization patterns, monitor exposed BIN ranges, and respond to higher volumes of fraud alerts and disputes. At scale, BIN attacks can also increase operational costs and place additional strain on fraud detection systems.
How to prevent BIN attacks
Businesses play the biggest role in preventing automated card testing, but cardholders can also reduce risk by monitoring unusual account activity.
For businesses
| Prevention measure | How it helps prevent BIN attacks |
| Velocity controls | Limit repeated authorization attempts within a short period, making large-scale testing harder |
| CAPTCHA and bot detection | Help block automated scripts used to test generated card details |
| Real-time monitoring | Helps detect spikes in low-value attempts, unusual decline rates, or repeated activity tied to the same BIN range |
| Address Verification Service (AVS), Card Verification Value (CVV) checks, and 3D Secure | Add verification steps that make the generated card details harder to validate |
| Device fingerprinting and traffic analysis | Help identify automated payment behavior and repeated attempts from the same device, IP address, or traffic pattern |
For cardholders
- Enable transaction alerts: Real-time alerts can help cardholders quickly spot suspicious activity.
- Consider identity monitoring tools: Services such as ExpressVPN’s Identity Defender can help cardholders monitor for certain fraud- or identity-related alerts. Identity Defender is currently available to eligible U.S. customers on Advanced and Pro plans, and included features may vary by plan.
- Review statements regularly: Checking account activity makes it easier to catch unfamiliar charges or repeated authorization attempts.
Report suspicious transactions immediately: Fast reporting gives the issuer a chance to investigate and restrict or replace the card if needed.
FAQ: Common questions about BIN attacks
Can a BIN attack happen without my physical card?
Are BIN attacks the same as card testing?
What are the signs of a BIN attack on my card?
What should I do if I see small test charges?
How do BIN attacks affect online merchants?
What is the difference between a BIN attack and a brute force attack?
Take the first step to protect yourself online. Try ExpressVPN risk-free.
Get ExpressVPN